HSTS configuration blocks Jira from redirect HTTP to HTTPs connections
Platform Notice: Data Center Only - This article only applies to Atlassian products on the Data Center platform.
Note that this KB was created for the Data Center version of the product. Data Center KBs for non-Data-Center-specific features may also work for Server versions of the product, however they have not been tested. Support for Server* products ended on February 15th 2024. If you are running a Server product, you can visit the Atlassian Server end of support announcement to review your migration options.
*Except Fisheye and Crucible
Symptoms
Application is not able to redirect connections after the redirect is configured following the steps on Running Jira applications over SSL or HTTPS.
There are no clear errors on the logs, the redirection just does not work and leaves the user with a black page.
Cause
HSTS headers (Strict-Transport-Security) are enforced in a few Jira releases (8.5.11, 8.13.3, 8.14.1, 8.15.0, 8.22.2) to address some security concerns.
Notes: The failing redirection is due to the fact that the Jira domain is added to HSTS domain security policies as Jira enforced the HSTS headers and it's hosted over non-default HTTP and HTTPS ports. This is prominent when we are using CA-signed SSL certificate (not a self-signed SSL certificate as HSTS requires the certificate to be a trusted certificate).
Notes: There are other reasons for HTTP to HTTPS restrictions such as redirect directives added in <Jira_Install>/conf/web.xml or <Jira_install>/atlassian-jira/WEB-INF/web.xml files. There are cases where the security constraints (like the directive "Restricted URLs") caused HTTPS redirection. Check these files against stock versions and ensure there are no directives that redirect traffic.
Refer the KB article Browser redirects other applications to HTTPS when using the same domain/subdomain as Jira for resolution steps if other applications deployed on the same Jira DNS are being forced to HTTPs by the browser.
Resolution
We do recommend using a proxy to make the redirections work, this would be the best approach for applications that are open to external connections.
Configure Jira server to run behind a NGINX reverse proxy
Diagnosis
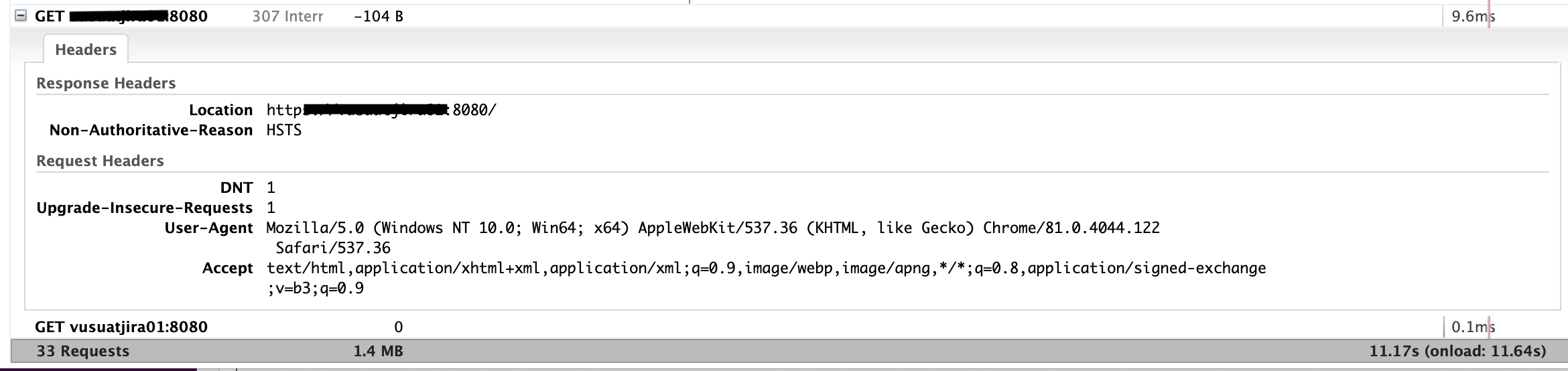
A HAR file taken during a redirection attempt will show us the redirection request receiving a 307 error and having the following HTTP headers.
Context
If a website accepts a connection through HTTP and redirects to HTTPS, visitors may initially communicate with the non-encrypted version of the site before being redirected, if, for example, the visitor types http://www.foo.com/ or even just foo.com.
The HTTP Strict Transport Security header informs the browser that it should never load a site using HTTP and should automatically convert all attempts to access the site using HTTP to HTTPS requests instead.
Workaround
For applications that are not open to external connections, we have a workaround that disables HSTS checks. To revert the behavior back to before, we can add the -Dcom.atlassian.jira.strict.transport.security.disabled=true JVM parameter to Jira as per Setting properties and options on startup.
After adding the JVM parameter and restarting Jira, it's also necessary for users to delete the HSTS configuration stored for the Jira domain (Base URL) from their browsers:
Chrome
Access chrome://net-internals/#hsts from the browser
Enter the domain that you want to remove in the Delete domain security policies section and click add
Try to access Jira again
Firefox
Start by closing any open windows.
Next, open your browsing history by clicking Ctrl + Shift + H.
Navigate your way to the site that your wish to clear the HSTS settings.
Right-click on the site and click on Forget About This Site.
Was this helpful?