Launch Bitbucket in AWS manually
The AWS Quick Start template as a method of deployment is no longer supported by Atlassian. You can still use the template, but we won't maintain or update it.
We recommend deploying your Data Center products on a Kubernetes cluster using our Helm charts for a more efficient and robust infrastructure and operational setup. Learn more about deploying on Kubernetes.
AWS now recommends switching launch configurations, which our AWS Quick Start template uses, to launch templates. We won’t do this switch, however, as we’ve ended our support for the AWS Quick Start template. This means you're no longer able to create launch configurations using this template.
This page describes how to launch the Bitbucket Amazon Machine Image (AMI) manually, giving you complete control over the components enabled in the AMI, and over AWS-specific configuration, network and security settings.
For an automated way to launch Bitbucket we recommend deploying your Data Center products on a Kubernetes cluster using our Helm charts. Learn more about deploying on Kubernetes.
While you can still deploy a multi-node Bitbucket Data Center instance using the AWS Quick Start guide, we no longer support or maintain Quick Start templates as a deployment method.
You can launch the Atlassian Bitbucket Server AMI directly from the AWS Console, or by running the EC2 launch wizard. See Launching EC2 Instances for detailed instructions.
The Bitbucket AMI
The Atlassian Bitbucket Server AMI provides a typical deployment of Bitbucket Server in AWS. It bundles all the components used in a typical Bitbucket Server deployment (reverse proxy, external database, backup tools, data volume, and temporary storage) pre-configured and ready to launch.
You can use the Atlassian Bitbucket Server AMI as a "turnkey" deployment of a Bitbucket Server instance in AWS, or use it as the starting point for customizing your own, more complex Bitbucket Server deployments.
Finding the Atlassian Bitbucket Server AMI
You can find the Atlassian Bitbucket Server AMI by clicking Community AMIs and searching for Atlassian Bitbucket.
Be sure to use the correct AMI ID for your specific region.
To find the latest AMI using the Amazon CLI you can use the following command:
aws ec2 describe-images --owners 098706035825 --filters "Name=name,Values=Atlassian Bitbucket*" --query 'sort_by(Images, &CreationDate)[-1].{ID:ImageId, "AMI Name":Name}' --output table The Bitbucket AMI is not currently available in some regions, such as govcloud-us (AWS GovCloud (US)) and cn-north-1 (China (Beijing)).
Components of the Bitbucket Server AMI
An instance launched from the Atlassian Bitbucket Server AMI contains the following components:
- Bitbucket Server (either the latest version or a version of your choice),
- an external PostgreSQL database,
- nginx as a reverse proxy,
- the Bitbucket Server DIY Backup utilities pre-configured for native AWS snapshots,
- an EBS Volume and Instance Store to hold the data.
| Operating system | Amazon Linux 64-bit, 2016.09.0 |
|---|---|
| Bitbucket Server | Bitbucket Server (latest public version or a version of your choice) is downloaded and installed on launch. |
| Administrative tools | atlassian-bitbucket-diy-backup pre-installed and configured for AWS native backup, accessible over SSH. |
| Reverse proxy | nginx, configured as follows:
|
| Database | PostgreSQL 9.3 |
| Block devices |
|
Choosing an instance type
When choosing an EC2 instance type, see Infrastructure recommendations for enterprise Bitbucket instances on AWS for recommended instance sizing.
 Minimum hardware requirements
Minimum hardware requirements
The default t2.micro (Free tier eligible), small, and medium instance types don't meet Bitbucket Server's minimum hardware requirements, and aren't supported for production deployments. See Infrastructure recommendations for enterprise Bitbucket instances on AWS for the EC2 instance types supported by Bitbucket Server.
Configure instance details
When configuring your EC2 instance there are some important details to consider:
Identity and Access Management (IAM) Role
IAM Role must be configured at launch time
An IAM Role can only be configured for your EC2 instance during initial launch. You can't associate an IAM role with a running EC2 instance after launch. See IAM Roles for more information.
It is recommended to launch your instance with an IAM Role that allows native AWS DIY Backup to run without explicit credentials. See IAM Roles for Amazon EC2 for more information.
While configuring instance details in the EC2 Launch wizard, you can create a new IAM Role by clicking Create new IAM role. The role should contain at least the following policy:
{
"Statement": [
{
"Resource": [
"*"
],
"Action": [
"ec2:AttachVolume",
"ec2:CreateSnapshot",
"ec2:CreateTags",
"ec2:CreateVolume",
"ec2:DescribeSnapshots",
"ec2:DescribeVolumes",
"ec2:DetachVolume"
],
"Effect": "Allow"
}
],
"Version": "2012-10-17"
}
Advanced Details
The Atlassian Bitbucket Server AMI can be configured in a number of different ways at launch time:
- The built-in PostgreSQL and Nginx components (enabled by default) can be disabled
- Self-signed SSL certificate generation (disabled by default) can be enabled
You can control these options supplying User Data to your instance under Advanced Details in Step 3: Configure Instance Details of the EC2 launch wizard. All user-configurable behavior in the Atlassian Bitbucket Server AMI can be controlled by creating a file /etc/atl containing shell variable definitions. On first boot, the Atlassian Bitbucket Server AMI will source the file /etc/atl (if it exists), allowing its built-in default variable definitions to be overridden.
For example, to enable self-signed SSL certificate generation (and force all Web access to Bitbucket Server to use HTTPS), you can add User Data (As text) as follows:
#!/bin/bash
echo "ATL_SSL_SELF_CERT_ENABLED=true" >>/etc/atlFor a complete list of variables that can be overridden in User Data at launch time, see Administer Bitbucket in AWS.
User Data is flexible and allows you to run arbitrary BASH commands on your instance at launch time, in addition to overriding variables in /etc/atl. See Running Commands on Your Linux Instance at Launch for more information.
 Security considerations
Security considerations
See Securing Bitbucket in AWS for more details about enabling HTTPS and self-signed certificates in the Atlassian Bitbucket Server AMI.
Add storage
When attaching EBS volumes, use these storage device settings for your instance.
| Type | Device | Purpose | Size (GiB) | Volume Type | IOPS | Delete on Termination |
|---|---|---|---|---|---|---|
| Root | /dev/xvda | Linux root volume | 50 | General Purpose (SSD) | N/A | Yes |
| EBS | /dev/xvdf | Bitbucket Server data: repositories, attachments, avatars, etc. | 100+ | General Purpose (SSD) / Provisioned IOPS * | 300+ * | Yes |
| Instance Store | /dev/xvdb | Bitbucket Server temporary files and caches | N/A | N/A | N/A | N/A |
* Provisioned IOPS with at least 500 – 1000 IOPS is recommended for instances with more than 500 active users. See Infrastructure recommendations for enterprise Bitbucket instances on AWS for more information.
The Atlassian Bitbucket Server AMI won't use any other block devices attached to the instance. The EBS volume for /dev/xvdf will be initialized and formatted at launch time, unless a snapshot id is provided (see the screen capture below), in which case it will only format it if it's not already formatted. See Managing EBS Volumes for more information about storage options in Amazon EC2.
Attach an existing EBS snapshot
You can also attach an existing EBS volume based on a snapshot during launch. To attach an existing EBS volume, within the Device field, change the EBS volume device to /dev/sdf and enter the Snapshot ID of the snapshot.
See Administering Bitbucket Server in AWS - Moving your Bitbucket Server data volume between instances for more details.
Configure your Security Group
When configuring your Security Group, you must allow allow incoming traffic to all the following ports. For more information, see Using Security Groups.
| Type | Protocol | Port | Description |
|---|---|---|---|
| SSH | TCP | 22 | SSH port, allowing access to administrative functions |
| HTTP | TCP | 80 | |
| HTTPS | TCP | 443 | |
| Custom TCP Rule | TCP | 7999 | Bitbucket Server SSH port for Git hosting operations |
What's next?
Now you're ready to configure your AWS version of Bitbucket Server.
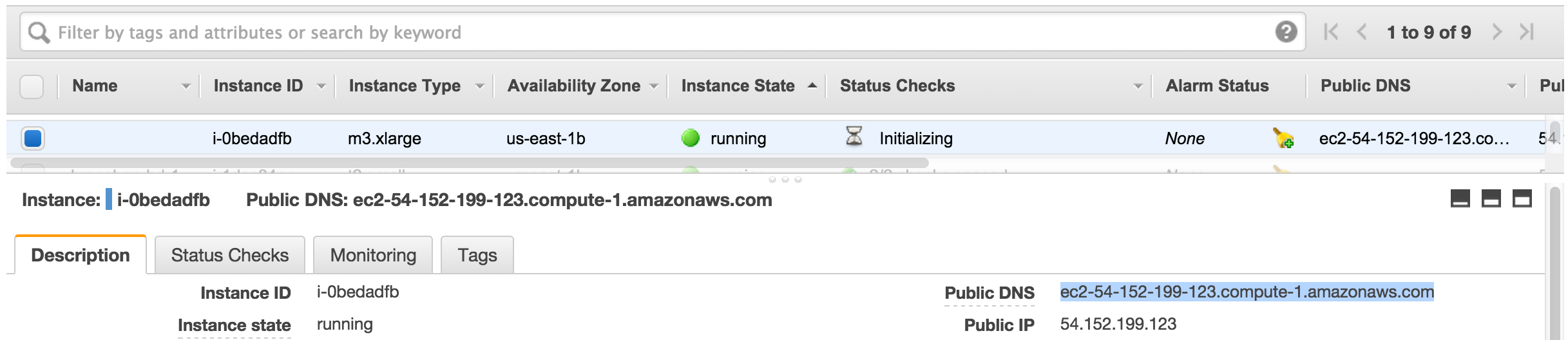
View your new instance
Once your new EC2 instance has launched, find it within the EC2 console and navigate to the URL provided so you can continue configuring Bitbucket Server.
To find the URL of your new EC2 instance
- From within the EC2 Console, in the Description tab of your new instance, copy the Public DNS.
- Paste the URL into a browser window to view start using Bitbucket Server.
Set up your AWS deployment of Bitbucket Server
Once you've followed the URL of the EC2 instance you are presented with the Bitbucket Server Setup Wizard. When you've completed the setup, you can use your instance like any other Bitbucket Server instance. So be sure to check out the rest of the Getting Started with Bitbucket Server documentation.