Using the SCP task in Bamboo
You can use the Bamboo SCP task to upload files from Bamboo directly to a remote server as part of a Bamboo job. The SCP task is able to copy multiple files and preserves the directory structure for the copied files.
See Configuring a deployment task for an overview of Bamboo deployment tasks.
Related pages:
To configure an SCP task:
- Navigate to the Tasks configuration tab for the job (this will be the default job if creating a new plan).
- Select the name of an existing SCP task, or click Add task > SCP Task to create a new task.
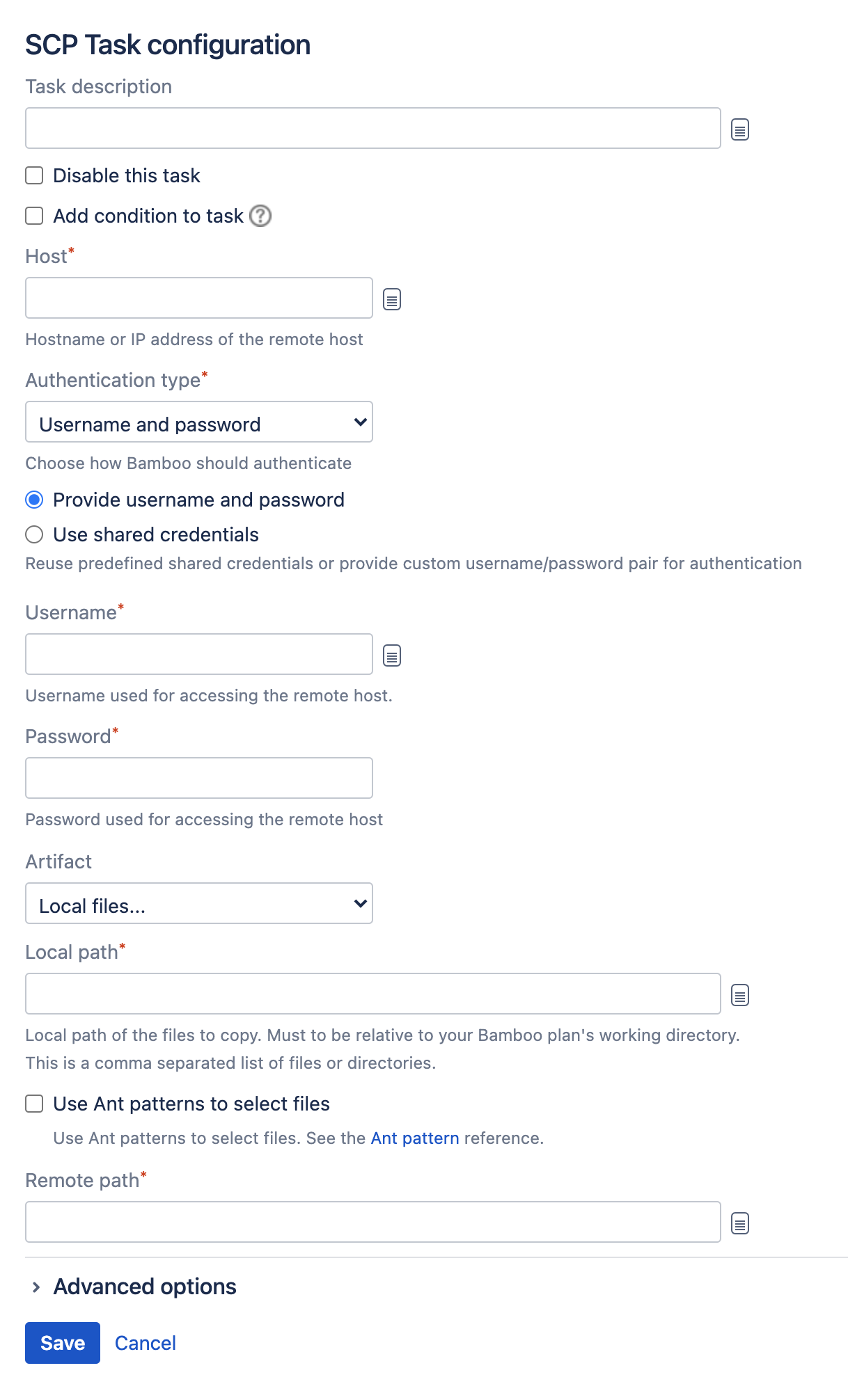
Complete the following settings:
Task description
Helps you identify the purpose of the task.
Disable this task
Check, or clear, to selectively run this task.
Add condition to task
Make task run only when a certain condition is met.
You can find conditions on Atlassian Marketplace or implement your own.
Host
The hostname or IP address of the remote server to which the files will be copied.
Verify remote host fingerprint on connect
Enter the host fingerprint to be verified. See below for more details.
Port
The port number of the remote host that is used for the SSH connection. The default value is 22.
Username
The username to use to connect to the remote host.
Authentication Type
Password – the password associated with Username.
Key without passphrase – browse to the SSH private key with which to authenticate with the remote host.
Key with passphrase – browse to the SSH private key, and supply the passphrase, to use to authenticate with the remote host.
Local Path
The local path (relative to the Bamboo working directory) to the files you want to copy. Use commas to separate files and directories. You can also use Ant-style pattern matching to include multiple files, such as**/target/*.jar.
Remote Path
The path to the destination directory on the remote server.- Select Save.
Host fingerprint
You can determine the fingerprint for a host by running:
ssh-keygen -l -F <HOSTNAME>The fingerprint is the part of the response shown in the screenshot below: