Set up additional SSH keys
On this page
Related content
- No related content found
| robots | noindex |
While using the same password on multiple sites makes your accounts less secure, most of the time you can use the same SSH key for multiple accounts. However, there are specific situations when you'll need to set up more than one SSH key:
- You have two different Bitbucket Cloud accounts. For example, if you have a work-related Bitbucket account and a personal Bitbucket account, each account must have its own SSH key.
- You're using two different computers to log in to the same account.
- You want to execute DVCS actions on a repository with a script that uses a public key with an empty passphrase, allowing it to run without human intervention.
Here are your options when setting up additional SSH keys:
| Windows | macOS | Linux | |
|---|---|---|---|
| Git | Terminal | ||
| Mercurial | Sourcetree | Terminal |
By this point, you should have already created at least one SSH key. This one SSH key is your default identity because it's the key that Bitbucket checks first when authenticating. If you don't have an SSH key, follow the steps on Set up an SSH key.
Set up additional SSH keys for Git
When using Git, you can use this section to create as many SSH keys as you need on Windows, macOS, or Linux.
Step 1. Prepare your default identity
Determine your Git clone URL.
$ git remote -v
origin git@bitbucket.org:teamsinspace/bitbucketspacestation.git(fetch)
origin git@bitbucket.org:teamsinspace/bitbucketspacestation.git(push)Update the remote URL with your Bitbucket username by replacing
git@bitbucket.orgwith<username>@bitbucket.org. For this step and the ones that follow, enter your username in place of<username>.$ git remote set-url origin <username>@bitbucket.org:teamsinspace/bitbucketspacestation.git
Step 2. Create additional SSH keys
Generate your new SSH key. In place of
<username>, enter the username of the Bitbucket account for which you're creating the SSH key.For Windows 7 or earlier
You can only enter
ssh-keygeninto the Git Bash window. It won't work in the Command prompt.$ ssh-keygen -f ~/.ssh/<username>
Generating public/private rsa key pair.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /Users/<username>/.ssh/<username>.
Your public key has been saved in /Users/<username>/.ssh/<username>.pub.
The key fingerprint is:
7a:9c:b2:9c:8e:4e:f4:af:de:70:77:b9:52:fd:44:97 <username>
The key's randomart image is:
+--[ RSA 2048]----+
| |
| |
| .|
| Eo|
| . S . ..|
| . . o . ... .|
| . = = ..o o |
| . o X ... . .|
| .ooB.o .. |
+-----------------+Add your new SSH key to your account. Make sure you're adding it to the right account.
$ ssh-add ~/.ssh/<username>
Step 3. Add the public key to your Account settings
Add each public SSH key into the corresponding account. If you have an account that you access from two different locations, add both keys to that account.
From Bitbucket, choose Personal settings from your avatar in the lower left.
The Account settings page opens.
Click SSH keys.
The SSH keys page displays. If you have any existing keys, those appear on this page.
Copy the contents of your public key file.
Windows: Open your
~/.ssh/<public_key>file and copy its contents.macOS: Copy the output to the clipboard with this command:
$ pbcopy < ~/.ssh/<public_key_file>Linux: Copy the output to the clipboard with this command:
$ cat ~/.ssh/<public_key_file>
From Bitbucket, enter a Label for your new key, for example,
Public key #2.Paste the copied public key into the SSH Key field:
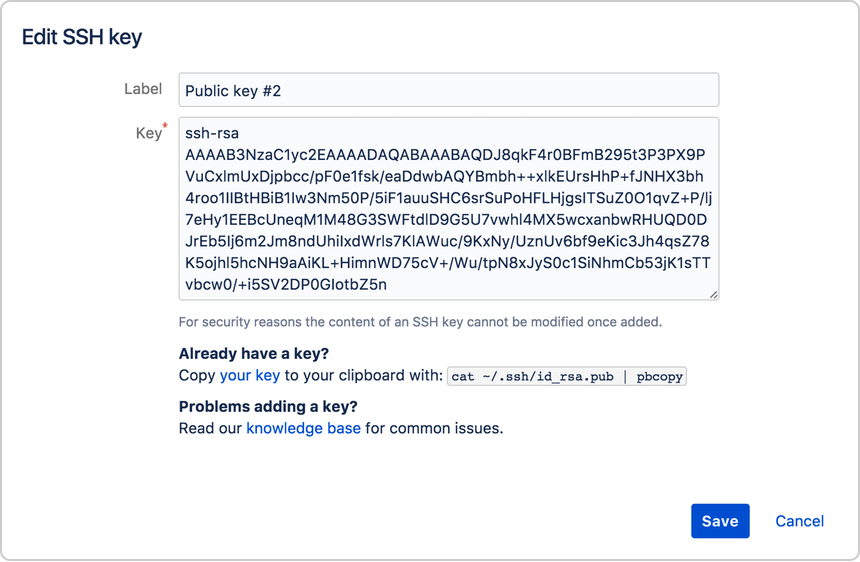
Click Save.
Bitbucket sends you an email to confirm the addition of the key.
Next time you clone a repository, use the SSH URL for that repository and replace git in the <username>@bitbucket.org part of the URL with your Bitbucket username. For example:
git clone <username>@bitbucket.org:teamsinspace/bitbucketspacestation.git
If you want to change the URL of an existing repository using HTTPS or a different SSH URL, change the remote URL for your repository.
Set up additional SSH keys for Mercurial (on macOS and Linux)
Use this section to create all additional keys for Mercurial or Linux. While you can use Sourcetree to generate your first SSH key on macOS, you must use the terminal to create additional keys.
Step 1. Prepare your default identity
Open the
.hg/hgrcfile and locate your Mercurial clone URL at thedefaultvalue.[paths] default = ssh://hg@bitbucket.org/teamsinspace/bitbucketspacestationUpdate the remote URL with your Bitbucket username by replacing
hg@bitbucket.orgwith<username>@bitbucket.org. For this step and the ones that follow, enter your username in place of<username>.[paths] default = ssh://<username>@bitbucket.org/teamsinspace/bitbucketspacestation
Step 2. Create additional SSH keys
Generate your new SSH key. In place of
<username>, enter the username of the Bitbucket account for which you're creating the SSH key.For Windows 7 or earlier
You can only enter
ssh-keygeninto the Git Bash window. It won't work in the Command prompt.$ ssh-keygen -f ~/.ssh/<username>
Generating public/private rsa key pair.
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /Users/<username>/.ssh/<username>.
Your public key has been saved in /Users/<username>/.ssh/<username>.pub.
The key fingerprint is:
7a:9c:b2:9c:8e:4e:f4:af:de:70:77:b9:52:fd:44:97 <username>
The key's randomart image is:
+--[ RSA 2048]----+
| |
| |
| .|
| Eo|
| . S . ..|
| . . o . ... .|
| . = = ..o o |
| . o X ... . .|
| .ooB.o .. |
+-----------------+Add your new SSH key to your account. Make sure you're adding it to the right account.
$ ssh-add ~/.ssh/<username>
Step 3. (Mercurial only) Enable SSH compression
Enabling SSH compression is recommended but not required.
By default, Git automatically performs compression when sending or retrieving data, but Mercurial doesn't. Enabling SSH compression can speed up sending and retrieving data, drastically in some cases.
To enable SSH compression:
- Open the Mercurial global configuration file (
~/.hgrc). Add this line to the UI section:
ssh = ssh -CWhen you are done the file should look similar to this:
[ui] # Name data to appear in commits username = Emma <emmap1@atlassian.com> ssh = ssh -C- Save and close the file.
Step 4. Add the public key to your Account settings
Add each public SSH key into the corresponding account. If you have an account that you access from two different locations, add both keys to that account.
From Bitbucket, choose Personal settings from your avatar in the lower left.
The Account settings page opens.
Click SSH keys.
If you've already added keys, you'll see them on this page.
In your terminal window, copy the contents of your public key file.
Mac OSX: Copy the output to the clipboard with this command:
$ pbcopy < ~/.ssh/<public_key_file>Linux: Copy the output to the clipboard with this command:
$ cat ~/.ssh/<public_key_file>
From Bitbucket, enter a Label for your new key, for example,
Public key #2.Paste the copied public key into the SSH Key field:
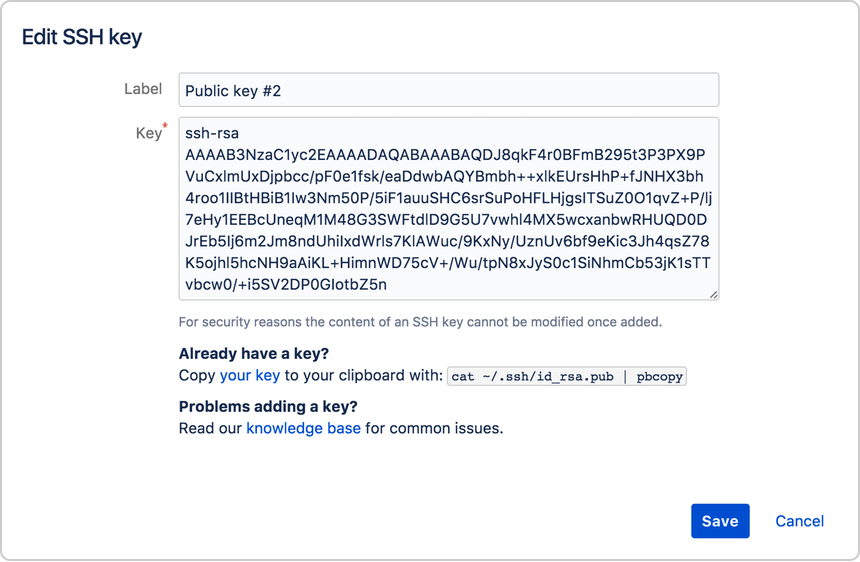
Click Save.
Bitbucket sends you an email to confirm the addition of the key.
Next time you clone a repository, use the SSH URL for that repository and replace hg in the <username>@bitbucket.org part of the URL with your Bitbucket username. For example:
hg clone ssh://<username>@bitbucket.org/teamsinspace/bitbucketspacestation
If you want to change the URL of an existing repository using HTTPS or a different SSH URL, change the remote URL for your repository.
Set up additional SSH keys with Sourcetree (on Windows)
Whether you use Git or Mercurial, use this section to create as many SSH keys as you need when using Sourcing on Windows.
Step 1. Create an SSH key
From Tools, select Create or Import SSH Keys.
From the PuTTY Key Generator dialog, click the Generate button.
As the SSH key generates, hover your mouse over the blank area in the dialog. It may take a minute or two.
When SSH key generation is complete, you see the public key and a few other fields.
Update the Key comment with something that distinguishes it from your other SSH keys.
Enter a passphrase for your SSH key in the Key passphrase and Confirm passphrase fields.
Click Save public key. From the save dialog, choose where to save your public key, name the file, and click Save.
Click Save private key. From the save dialog, choose where to save your private key, name the file, and click Save.
Close the PuTTY Key Generator dialog.
Step 2. (Mercurial only) Enable SSH compression
Enabling SSH compression is recommended but not required. You'll need to clone and open a Mercurial repository to complete these steps.
By default, Git automatically performs compression when sending or retrieving data, but Mercurial doesn't. Enabling SSH compression can speed up sending and retrieving data, drastically in some cases.
To enable SSH compression:
- Click Settings in the top right of the repository window.
The repository settings may open to the Remotes tab. If not, click the Remotes tab. - Click Edit Config File to open the Mercurial global configuration file (
~/.hgrc). Add this line to the UI section:
ssh = ssh -CWhen you're done the file should look similar to this:
[ui] # name and email (local to this repository, optional), e.g. username = Emma <emmap1@atlassian.com> ssh = ssh -CSave and close the file.
Step 3. Install your private key on Pageant
Sourcetree comes with an SSH authentication agent called Pageant. Load your private key into Pageant to automatically authenticate so that you don't need to enter your passphrase.
Double-click the Pageant (PuTTY Authentication Agent) icon in your system tray to open the Pageant Key List dialog.
Click the Add Key button.
The system displays the Select Private Key File dialog.
Navigate to the private key file you saved in Step 1 and click Open.
Enter the passphrase for your SSH key and click OK.
Pageant shows your key in the running list.
Press Close to close the dialog.
Step 4. Add the public key to your Account settings
From Sourcetree, open the PuTTY Key Generator dialog by going to Tools > Create or Import SSH Keys.
Click Load, navigate to your SSH folder, and click the private key.
Enter your passphrase for the SSH key and click OK.
Copy the public key in the first field.
From Bitbucket, choose Personal settings from your avatar in the lower left.
The Account settings page opens.
Click SSH keys.
If you've already added keys, you'll see them on this page.
Click Add key.
From Bitbucket, enter a Label for your new key, for example,
Public key #2.Paste the copied public key into the SSH Key field.
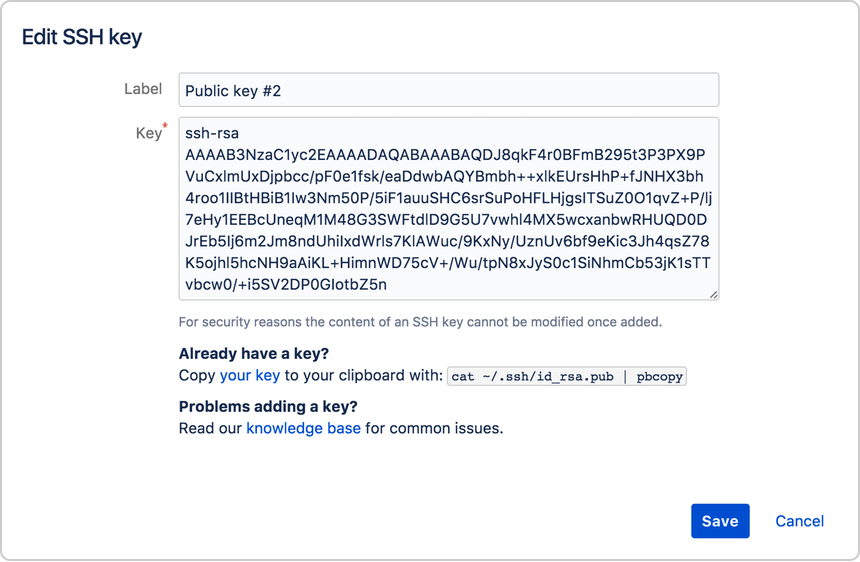
Click Save.
Bitbucket sends you an email to confirm the addition of the key.Edit an SSH key
After you add a key, you can edit the key's Label but not the key itself. If you need to change the key's contents, you must delete and re-add the key.
Related content
- No related content found