Security headers in Jira
Platform Notice: Data Center - This article applies to Atlassian products on the Data Center platform.
Note that this knowledge base article was created for the Data Center version of the product. Data Center knowledge base articles for non-Data Center-specific features may also work for Server versions of the product, however they have not been tested. Support for Server* products ended on February 15th 2024. If you are running a Server product, you can visit the Atlassian Server end of support announcement to review your migration options.
*Except Fisheye and Crucible
Purpose
To prevent clickjacking, Jira adds the X-Frame-Options and Content-Security-Policy security headers to each HTTP response. The headers block the content from being embedded in iframes, which might also affect pages that you want to be displayed in this way. If you don't like this change, you can create a list of paths to be excluded from this protection or disable the security headers.
Security headers
Jira 7.6-8.15
The following headers have been introduced with Jira 7.6. You can read the original bug report here: JRASERVER-25143 - Enable X-FRAME-Options header to implement clickjacking protection
| Header | Value |
|---|---|
| X-Frame-Options | SAMEORIGIN |
| Content-Security-Policy | frame-ancestors 'self' |
Jira 8.16 and later
In Jira 8.16 and later, the following header is introduced for security purposes: Content-Security-Policy: sandbox.
The sandbox directive enables a sandbox for a requested resource that is similar to the <iframe> sandbox attribute. It applies restrictions to an object's actions including preventing pop-ups, executing plugins and scripts, and enforcing a same-origin policy.
By default, the sandbox policy is enabled and applied:
To all content types except for
text/html,application/javascript, andtext/javascript. These can’t be sandboxed.When the content-disposition header is set to
attachment.
The default parameters can be tweaked by changing the following properties.
Property | Description |
|---|---|
| Indicates the original media type of the resource |
| Indicates if the content will be displayed inline in the browser, on a web page, or as an attachment that can be downloaded |
To modify the default properties:
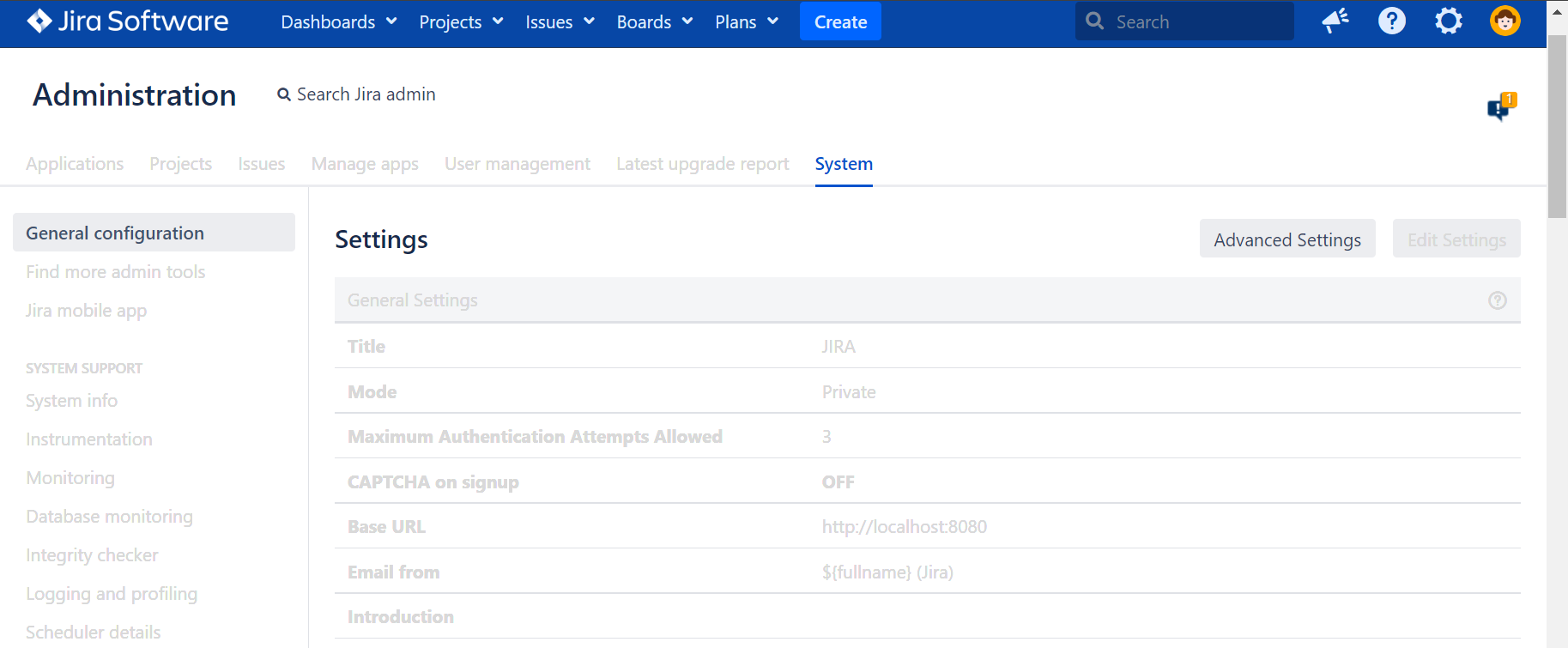
- Go to Administration > System > General configuration and select Advanced Settings.
- Edit the values of the properties.
Additionally, we’ve added new properties that allow for configuring what clauses will be sent to what browsers and what paths should have such differentiation. This prevents failures when audio or video attachments are playing in some browsers.
Check the new properties.
Property | Description |
|---|---|
| You can’t see it in the user interface. By default, paths that have differentiated clauses are A Jira admin can specify additional paths only in the |
| It’s visible only to a System admin in Advanced settings in General configuration of the Jira instance. The property allows for appending suffixes required by browsers. For example, Chrome needs If any new bugs in browsers appear, the System admin can tweak this behavior for supported browsers. The default value for this property is: |
Solution
Excluding paths
To create a list of paths excluded from the protection, use the com.atlassian.jira.clickjacking.protection.exclude system property and separate the paths with a comma. For example:
-Dcom.atlassian.jira.clickjacking.protection.exclude=/rest/my-plugin/1.0/dashboard,/rest/collectors/1.0/template/form/For more info on how to apply this, see Setting properties and options.
Determining which paths to exclude
The easiest option is to examine the access logs from Jira. For example, if you have a report in Jira and want to display it in Confluence:
Add an iframe with the Jira report into Confluence and reload the page. In this example, the iframe URL is used. The report will fail to load. You can see this in the screenshot.
http://localhost:8080/jira/secure/RapidBoard.jspa?rapidView=1&projectKey=SA&view=reporting&chart=cumulativeFlowDiagram&swimlane=1&column=4&column=5&column=6- Confluence will attempt to make several requests to Jira for the information needed to display the report. Due to the security headers, the report will fail to load.
Check Jira's access logs to see what URI endpoints were requested by Confluence. These are the paths you want to exclude. In this example, corresponding traces in the access logs are the following:
0:0:0:0:0:0:0:1 i639x1086x1 admin [19/Aug/2022:10:39:44 +0200] "GET http://localhost:8080/jira/secure/RapidBoard.jspa HTTP/1.1" - - - "http://localhost:8090/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.0.0 Safari/537.36" "1jv33ya" 0:0:0:0:0:0:0:1 o639x1086x1 admin [19/Aug/2022:10:39:44 +0200] "GET http://localhost:8080/jira/secure/RapidBoard.jspa HTTP/1.1" 200 8698 0.0260 "http://localhost:8090/" "Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/104.0.0.0 Safari/537.36" "1jv33ya"Add the endpoint from the access logs to the system property. Learn more in Setting properties and options.
JVM_SUPPORT_RECOMMENDED_ARGS="-Dcom.atlassian.jira.clickjacking.protection.exclude=/secure/RapidBoard.jspa"- Restart Jira and attempt to load the iframe in Confluence. It will successfully display now.
Excluding paths in plugins
Jira 7.7 or later.
If you develop plugins for Jira and use iframes on purpose, you can also exclude paths on a Jira instance that uses your plugin.
To do this, add the paths to be excluded by adding the following code to the atlassian-plugin.xml file.
<clickjacking-http-headers-excluded-paths key=“some-unique-key-for-this-module”>
<path>/plugins/servlet/reference-servlet-with-filter</path>
<path>/plugins/servlet/other-servlet</path>
</clickjacking-http-headers-excluded-paths>For more info, see this Java document.
Disabling security headers
To disable the X-Frame-Options and Content-Security-Policy security headers, set the system property com.atlassian.jira.clickjacking.protection.disabled to true.
Steps to disable X-Frame-Options and Content-Security-Policy
- From
<jira-install>/bin, open setenv.bat (for Windows) or setenv.sh (for Linux). - Find the section set JVM_SUPPORT_RECOMMENDED_ARGS=.
- Add the following code into to the section -Dcom.atlassian.jira.clickjacking.protection.disabled=true.
The full argument should look as follows:
set JVM_SUPPORT_RECOMMENDED_ARGS="-Dcom.atlassian.jira.clickjacking.protection.disabled=true"
- Restart Jira to load the new argument.
For more information on how to apply this, see Setting properties and options.
Disabling Content-Security-Policy: sandbox
To turn off Content-Security-Policy: sandbox completely, set the feature flag jira.security.csp.sandbox.disabled.