Configure an outgoing link
When you configure an outgoing link to an external application, Jira requests data from this application, which means that it acts as the OAuth client. This type of link is primarily used in Jira to create the OAuth 2.0 integration for popular mail servers. To learn more about the type of links and additional details, see Link to other applications.
OAuth 2.0 for SMTP outgoing mail servers is supported in Jira 9.2 and above.
We keep the support for Google and Microsoft as providers, as well as the IMAP, POP3, and SMTP protocols for connection for Jira versions 8.22 to 9.1.
When to use it
We’ve created an outgoing OAuth 2.0 integration primarily because Google and Microsoft announced deprecating basic authentication. This means you wouldn’t be able to use these providers (Gmail, Microsoft Exchange Online) to let users create issues and comments from emails if you were authenticating using basic auth. To fix this, you need to configure the OAuth 2.0 integration with these providers, and then update the configuration of your mail servers.
You don’t need to take any actions if you’re using IMAP or POP3, these will continue to work.
Before you begin
You need to ensure the following:
Your server needs to run over HTTPS. If it doesn’t, you will not be able to configure OAuth 2.0.
Your base URL needs to be configured correctly. This is important as the redirect URL you’ll need to provide is based on Jira’s base URL.
Create an outgoing link using application links
To create an outgoing link:
- In the upper-right corner of the screen, select Administration > Applications.
- Under the Integrations (the left-side panel), select Application links.
Select Create link.
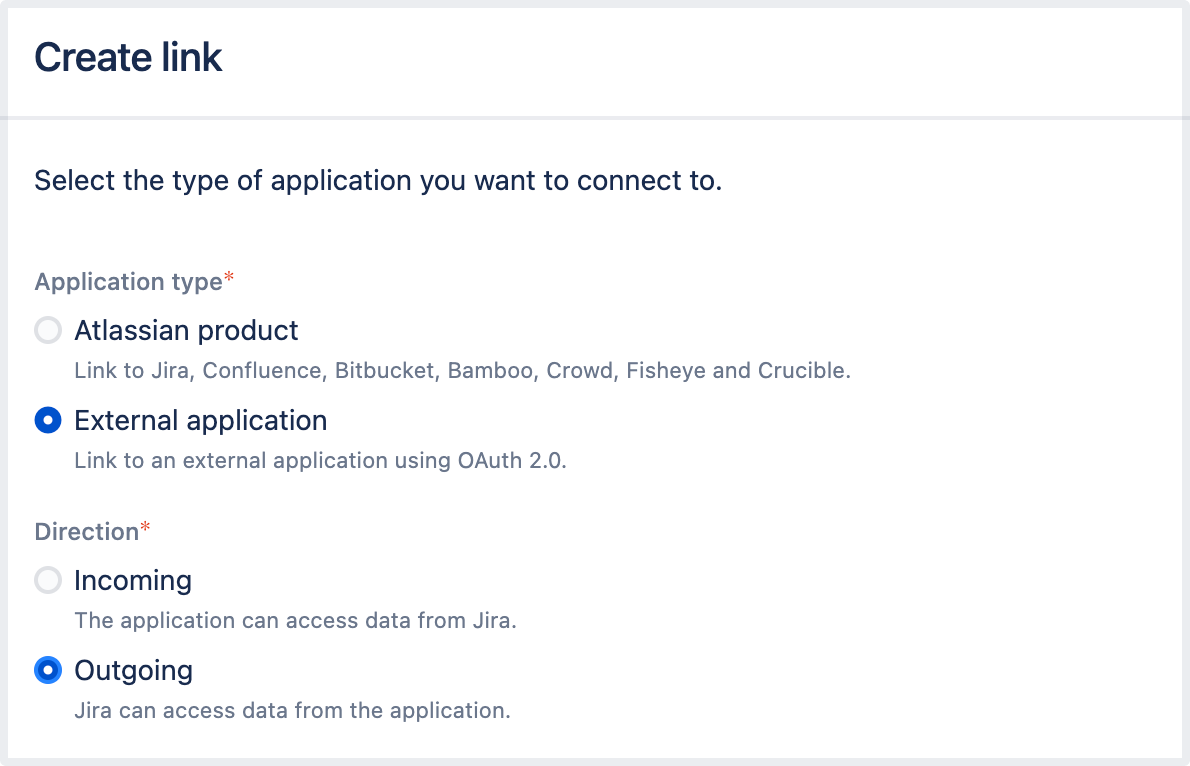
In a new dialog that opens, select External application, and then choose Outgoing as the direction.
Fill in the details as described in the following sections.
Configure your outgoing link
Follow these steps to configure your link:
1. Choose a service provider
Choose one of the following providers that you want to configure. Choosing Google or Microsoft lets you create an OAuth 2.0 integration for mail servers – in this case, some of the fields will be pre-filled:
Google
Microsoft
Custom (for internal tools or other providers)
2. Copy the Redirect URL and register it in your external application
Copy the Redirect URL and register it in your external application to obtain the client ID and client secret required to complete the configuration.
If you’re using Google or Microsoft as service providers, you’ll be able to copy the Redirect URL right away. For custom providers, you need to first provide the Authorization endpoint and Token endpoint. For more information on registering the URL with Google or Microsoft, check out the following guides:
Different providers might have different requirements related to the redirect URL. For example, Google doesn't allow it to be a private IP address. Make sure you provide an external URL (for example, of a load balancer for Jira Data Center).
3. Provide remaining application details
Provide the remaining details. Here you can find descriptions for all the fields.
| Name | Description |
|---|---|
Client ID | The client ID that's generated by the external application after registering Jira’s Redirect URL. This is the public identifier of the application. |
Client secret | The client secret that's generated by the external application after registering Jira’s Redirect URL. This is the shared secret between Jira and the application, which ensures the authorization is secure. |
Scopes | The required OAuth 2.0 scopes (permissions) that control what Jira can do in the external application. You need to specify different scopes for email servers. For Google, we recommend this scope: For Microsoft, we recommend that you always use the
For more information about scopes available in Google and Microsoft, see the detailed information at the Microsoft & Google sites. |
Authorization endpoint | The HTTPS URL where authorization to use OAuth 2.0 is started. |
Token endpoint | The HTTPS URL where refresh token requests are sent. As OAuth 2.0 tokens have an expiry, Jira will periodically update the token. |
Redirect URL | The Redirect URL that must be registered in the external application to obtain its client ID and client secret. This redirects the authentication flow back to Jira. |
4. Save your outgoing link
After you save the link, it will appear on the list together with other application links. You will now be able to select this link when configuring mail servers, DVCS accounts, or Jira Service Management email channels.
Next steps
You can use your link in the following built-in functionalities in Jira:
Troubleshooting
If you're facing some issues while configuring outgoing links for applications, check out the following articles: