Grant repository access to users and groups
When you create a repository, you specify whether it's private or public. If your repository is public, anyone can access it. If your repository is private, you can grant access to individuals and groups of users.
To create groups, go to the User Groups page of your workspace Settings.
If you create a new group for a workspace, Bitbucket doesn't automatically add it to the workspace's existing repositories. Alternatively, if you create a new group from your workspace, Bitbucket does automatically add it to your personal repositories.
Users and groups have one of the following access levels:
| Admin | Allows users to do everything within the repository: change repository settings, update user permissions, and delete the repository. |
| Write | Allows users to contribute to the repository by pushing changes directly. |
| Read | Allows users to view, clone, and fork the repository code but not push changes. Read access also allows users to create issues, comment on issues, and edit wiki pages. |
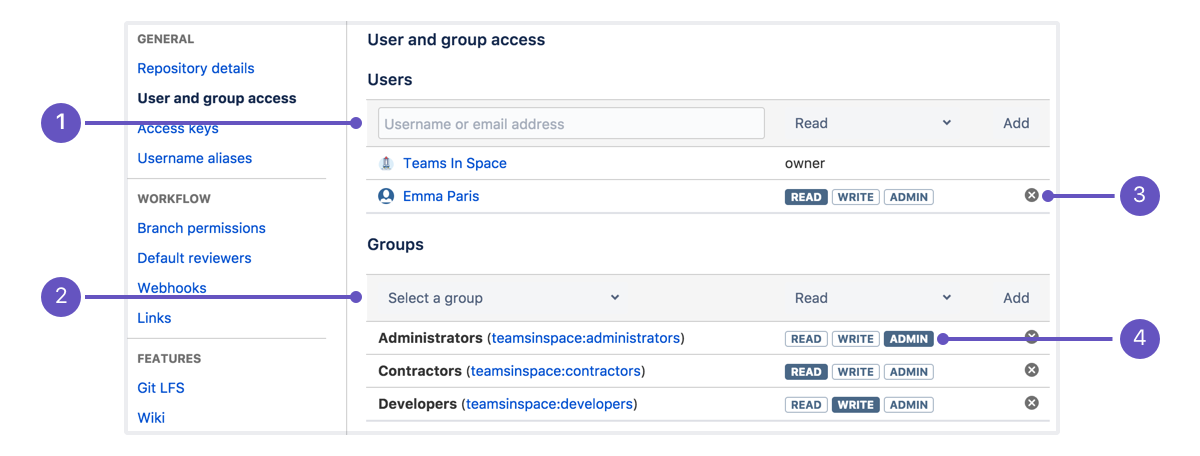
- User access: Enter a user and access type to add a user to a repo.
- Group access: Pick a group and access type to add a group to a repo.
- Remove: Click to remove access for a user or group.
- Change access: Click any of the access types to change access for a user or group.
If a user deletes his or her account, Bitbucket automatically deletes that user from all repository access lists.
When you add users
If you're on the Free plan and the number of users with access to your private repositories goes over 5, access becomes read-only until you upgrade your account or remove users from a group or individual repositories. You and other repository administrators still have access to the repository. For information on plan limits, see Bitbucket Cloud plan details.
Can I add a workspace?
You can't add a workspace to your repository. The only workspace with access is the workspace that owns the repository, but you can transfer repositories to your workspace if necessary. Or create a new group and add the specific users you want to that group.
Add group access to a repository
When you create a repository, Bitbucket checks to see if the repository's owner has any groups with an access level of read, write, or admin. If the workspace does, Bitbucket adds those groups to the new repository with the default permission. If a group has no access, that group does not appear on the User and group access page. However, you can still just add that group with the appropriate access.
To grant group access to a repository:
- From the User and group access page, click Select a group and scroll down to your new group or start typing its name in the text box.
- After you've selected the right group, select the appropriate access level from the access dropdown menu.
- Click Add to add the group to the repository.
Update user or group access
To update group access, click a different access level for the group from the User and group access page.
When you change group access or remove a group from a repository, you establish repository-level group settings. These changes remain in effect for the specific repository, even if you later change the group's access from the account or workspace's User groups page.
Add user access to a repository
While user groups are the best way to manage access to your repositories, you can also add users individually. To add individual users to your repository:
- From the User and group access page, enter a Bitbucket user's name or email address in the Users text box.
- Select an access level from the dropdown menu.
- Click Add.
If you add the email address of someone without an account, that person receives an email prompting him or her to create one. Once the user has Bitbucket access, he or she can access the repository.