Crowd 1.1.0 Release Notes
The Atlassian Crowd team is proud to announce the release of Crowd 1.1.
This release contains a whole host of new features targeted at implementing OpenID, along with core updates to the Crowd Administration Console.
OpenID-enable your organization with CrowdID
OpenID enables you to use a centralized identity to login to any website that supports OpenID. It opens up the possibilities of massive scale cross-domain SSO.
Think about all the accounts you have online: blogs, wikis, to-do lists, photo galleries. The list is endless. Even simple tasks such as leaving comments on someone else's blog may require you to register an account with that particular blogging system. This leaves you, as an end user, to set up and manage numerous accounts on each of these sites. With OpenID, rather than managing all these disparate accounts individually, users can manage their identity in one place via an authentication server.
With the ever-increasing adoption of this open authentication framework, including names such as Microsoft, AOL, Sun, Verisign and Firefox, expect to see many applications enabled for OpenID authentication.
CrowdID offers OpenID to an organization's user base, allowing users to manage their online identity. Everything from configuring different profiles, managing trusted sites to reviewing authentication activity, is accessible from CrowdID. Administrators can set up whitelists/blacklists so that only trusted hosts can request authentication and can set up secure communication via SSL. All of the users can be managed via Crowd's security server, utilizing LDAP services from products such as Microsoft Active Directory.
Included with CrowdID is a sample OpenID client application, providing a working example of an OpenID enabled application. This will help developers kick start OpenID-enabling their applications.
Using OpenID
Rather than registering and typing in your username and password on each site that you visit, OpenID allows you to type a URL similar to 'openid.mycompany.com/users/jstepka':
The OpenID website that you are logging in to will redirect you to CrowdID, which will ask you if you would like to allow authentication with the requesting site.
You can even choose to 'Always' allow authentication with particular OpenID sites, which allows pass-through authentication if you are already logged into your CrowdID server. If you do this, then when you visit the site later, simply provide your URL (e.g. 'openid.mycompany.com/users/jstepka') and you are in.
Think of it as 'Remember Me' for the whole internet!
'Blacklist' and 'Whitelist'
'Blacklists' and 'whitelists' allow administrators to lock down CrowdID their server so that, if necessary, it can only communicate with trusted hosts with which you have established relationships.
A blacklist will prevent specific hosts from communicating with the OpenID server. A whitelist will allow only specific hosts to communicate with the OpenID server.
OpenID Advanced Options
Some external sites implement security better than others. With CrowdID, you can pick how tough you want to be on OpenID sites that communicate with your Crowd OpenID server.
Crowd Console and Server Updates
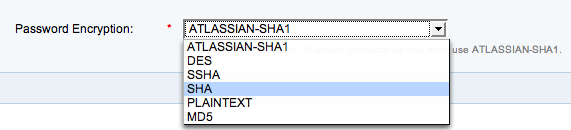
Choose Your Encryption Type
Every administrator has their own password policies. When using a Crowd Internal Directory you can now select the level of encryption you need.
Import Your JIRA and Confluence Passwords
Migration can be a pain. To ease your switch from existing Atlassian products, Crowd can now import your existing passwords!
Faster Web-Services
Crowd web-services now support GZip compression, improving the performance when downloading large amounts of data such as the all the members of a large group or when performing large search.
Improved Apache and Subversion Integration
The Apache and Subversion library performance has been improved with the implementation of client-side caching of approved authentication requests.
Jive Forums 5.5 Support
The Jive Forums centralized authentication connector has been updated to support the new 5.5 major release of Jive Forums.
LDAP Configuration Tester
When setting up a Crowd LDAP connection you can now verify that your configuration connects as expected.
JIRA Issue Tracker
Cheers,
The Atlassian Crowd Development Team